Finding The Nonce
Finding The Nonce
- A nonce is a "number only used once" abbreviation, which is inserted to a hashed-or encrypted-block in a blockchain in connections with crypto-currency mining that complies with difficulties level limitations when rehabilitated.
- The nonce is the number for which blockchain miners solve their problems. In exchange for the answer, bitcoin is provided to the blockchain mining companies.
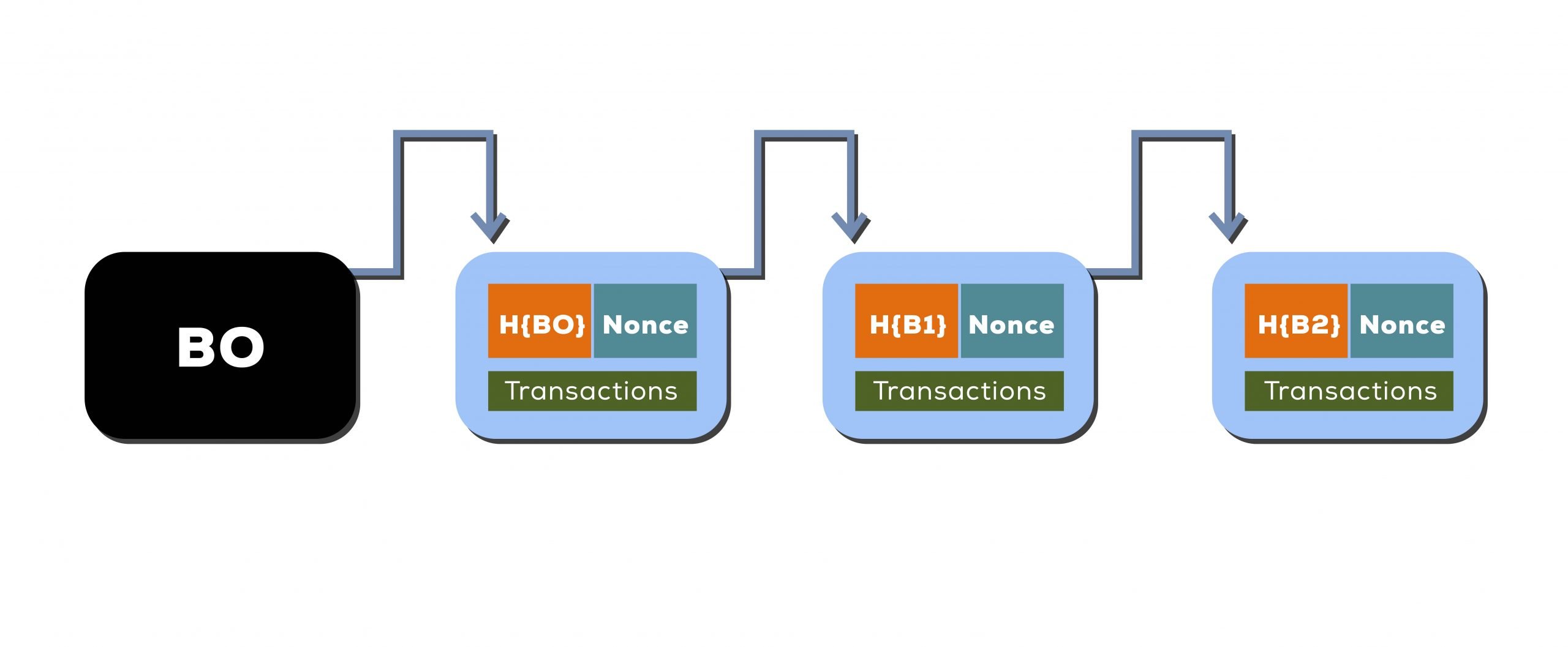
- The crypto-currency blockchain is the cornerstone. Data from earlier blocks are either encoded or "hashed" into a number of numbers and characters in order to make the blockchain safe. This is done by using a function that provides a fixed length output to process the block input.
- The task used to build the hash is decisive, so that each time the same input is utilised it produces the same output.
- It implies that the function may effectively produce a hashed input, makes it difficult (to make the security of blockchain) to determine the input, and transforms the input to a very different hash. This sophisticated mechanism forms the blockchain data protection network.
- To choose the string to use as the nonce a lot of trial and error is required, as it is a random string. A miner has to devise a nonce, add it to the current header hash, add the value again and compare it to the destination hash. The miner has produced a solution and is given the block if the resulting hash value satisfies the conditions.
- It is quite unlikely for a miner to devise the nonce correctly in the first try, so that the miner can possibly test a great number of nonce alternatives before he can get it right. The more complex it is — a measure of how tough it is to produce a hash that is less than the objective — the longer it takes to provide a solution.
- The difficulty of the block is maintained throughout the whole network, which allows all miners to find the right hash. In the normal case, cryptocurrency networks define a goal number of blocks to be processed over a particular period of time and change the difficulty regularly to guarantee that this aim is fulfilled.
- If this objective is not met in the number of blocks processed, then the difficulty is lowered, as the time restriction is reduced to the amount of time.
Use For Nonce
Nonce are employed with a number of networking computer applications, including buying authentication, two-factor authentication and other account recovery and identification applications, electronic signatures, data encryption and more.





